Where This Goes
Start with read-only tools. Prove they work. Then let agents do more.
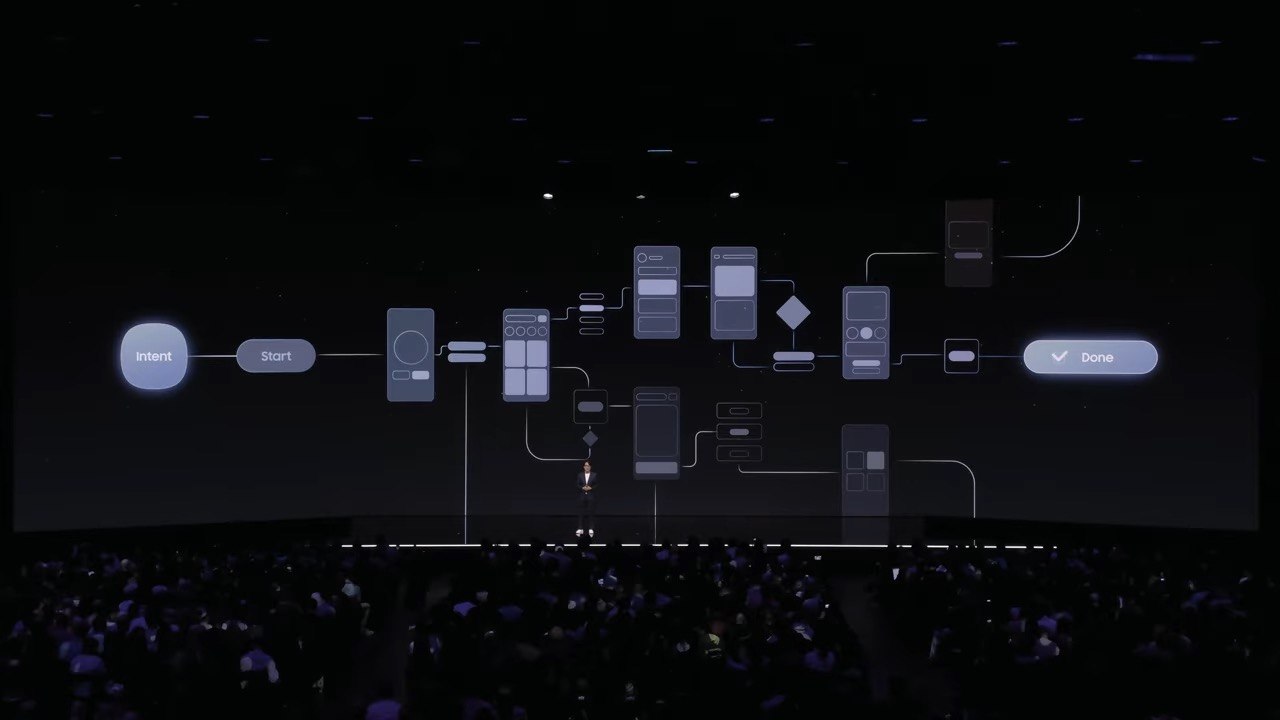
The Agentic Roadmap
Informational
AI agents can search restaurants, check availability, and view details on behalf of the cardholder. No actions are taken. The agent is purely a research assistant for dining decisions.
Assistive
The agent can suggest options and place temporary holds, but the cardholder always confirms. The hold pattern is the safety mechanism: nothing commits without human approval. This is where we prove the trust model works.
Fully Agentic
With established trust and proven safety patterns, AI agents can book, modify, and cancel reservations autonomously. The cardholder sets preferences and constraints ("Italian, under $50pp, near my hotel") and the agent handles the rest, including rebooking if plans change.
Agent-to-Agent Coordination
The Amex agent doesn't operate alone. It coordinates with airline agents, hotel agents, and restaurant agents to orchestrate complete travel experiences. "Book dinner near my hotel the night before my morning flight" becomes a multi-agent conversation.
This Is Already Happening
Samsung's Galaxy S26 shipped with Gemini agent control in February 2026. The OS-level agent layer is here. Without an MCP server, these agents screen-scrape. With one, they get structured, permissioned access.
Samsung Unpacked February 2026: Gemini agent ordering food and booking rides on Galaxy S26
The Strategic Insight
Whoever figures out the trust model for agent-initiated financial actions first wins the agentic finance space. Amex is uniquely positioned: you already have the cardholder trust, the merchant relationships, and now with Resy, the platform to prove it works.
Why Resy Is the Right Starting Point
✔ Bounded Transaction Size
Restaurant reservations are low-to-medium stakes ($50-$500 deposits). Perfect for building trust in agent-initiated financial actions before expanding to higher-stakes domains like travel or shopping.
✔ Clear Reversibility
Cancellation policies are well-defined and time-bound. If an agent makes a mistake, the blast radius is contained and the remedy path is clear.
✔ High Intent Signal
When someone asks an AI to book a restaurant, the intent is unambiguous. Compare this to "buy me something nice": dining has structured inputs (date, time, party size) that reduce agent error.
✔ Owned Platform
Amex owns Resy. You control the API surface, the data model, and the trust boundaries. No third-party dependency for the initial proof of concept.
Resy is the proving ground. The patterns you build here (hold-before-commit, scoped OAuth for agents, cardholder re-confirmation for financial actions) become the template for agentic experiences across every Amex product: travel, shopping, financial planning. It all starts with "Book me a table for two on Friday."